Delhi Police Busts APK Malware Cyber Fraud Racket; Bihar-Based Accused
Arrested After Multi-State Investigation
In a major breakthrough against rising cybercrime incidents in India, the Cyber Cell of the Delhi Police has arrested a 23-year-old man from Bihar for allegedly operating a sophisticated cyber fraud racket that used malicious APK files to compromise victims’ mobile phones and siphon money directly from their bank accounts.
The accused, identified as Vikas Kumar Gupta, was allegedly part of an organized network involved in digital banking fraud, illegal fund transfers, and malware-based mobile hacking. Investigators claim the gang targeted unsuspecting users by tricking them into installing harmful APK applications on their Android devices, giving cybercriminals unauthorized access to sensitive banking information.
The arrest highlights the rapidly growing threat of APK malware scams in India, where fraudsters increasingly rely on social engineering and remote-access malware to steal money within minutes.
How the Cyber Fraud Came to Light
The case surfaced after a delivery executive filed a complaint through the National Cyber Crime Reporting Portal (NCRP). According to police officials, the victim noticed suspicious activity on his mobile phone after an unknown APK application was automatically installed or downloaded onto his device.
Within a short span of time, approximately ₹2.48 lakh was fraudulently withdrawn from his bank account.
Following the complaint, the Cyber Police Station North registered an FIR and initiated a technical investigation to trace the source of the unauthorized transaction.
Police officials stated that cyber experts immediately began:
- Analyzing transaction records
- Tracking digital payment trails
- Monitoring linked bank accounts
- Identifying device connections and SIM activity
The investigation eventually led authorities to Bihar, where part of the stolen money had allegedly been transferred.
Money Trail Helped Police Trace the Accused
During forensic examination of banking transactions, investigators discovered that nearly ₹2 lakh from the victim’s account had been routed to a bank account in Bihar’s Utkarsh Bank.
The account was reportedly registered in the name of Vikas Kumar Gupta, a resident of Chhapra district in Bihar.
A special team from Delhi Police traveled to Chhapra to arrest the suspect. However, officials claimed that the accused had absconded before police arrived, and family members allegedly did not cooperate with investigators.
After weeks of technical surveillance, mobile tracking, and digital intelligence gathering, police finally located the accused in Delhi and took him into custody.
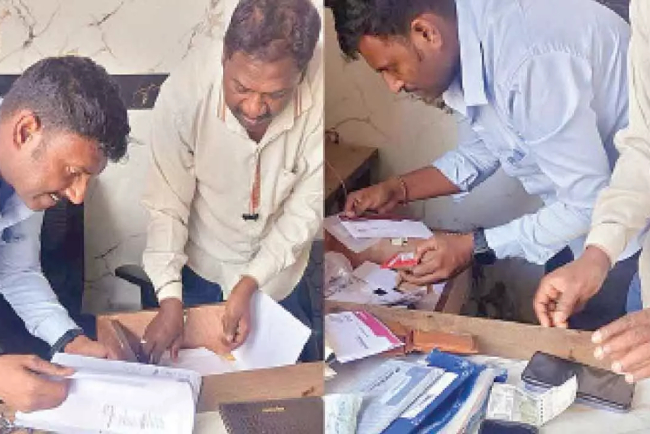
Authorities recovered:
- A mobile phone
- SIM cards
- Digital evidence linked to financial transactions
The seized devices are currently being examined for further leads and possible links to a larger interstate cybercrime network.
How the APK Malware Scam Worked
Investigators revealed that the gang allegedly relied on malicious APK files to gain access to victims’ smartphones.
What is an APK File?
APK (Android Package Kit) is the installation file format used by Android devices to install applications. While legitimate apps are generally downloaded through the Google Play Store, cybercriminals often distribute modified APK files through:
- WhatsApp messages
- SMS links
- Telegram channels
- Fake customer support calls
- Fraudulent banking alerts
- Delivery or KYC update links
Once installed, these applications can secretly request dangerous permissions from user
Possible Functions of the Malware
Cybersecurity experts believe such malware applications are commonly designed to:
| Malware Capability |
Purpose |
| Screen monitoring |
Capture banking activity |
| SMS access |
Read OTPs and alerts |
| Accessibility permissions |
Control device remotely |
| Keylogging |
Steal passwords and PINs |
| Remote access tools |
Operate apps without user knowledge |
| Contact access |
Spread scam links further |
In many cyber fraud cases, victims unknowingly grant permissions that allow hackers to completely monitor or control the phone.
Accused Allegedly Built His Own Cybercrime Network
According to police interrogation reports, the accused initially worked at a lower level in cybercrime operations by renting or supplying bank accounts to other fraudsters in exchange for commission.
Such accounts are commonly known as “mule accounts” and are used to temporarily store stolen money before transferring it across multiple channels to avoid detection.
However, officials stated that the accused later attempted to increase profits by creating his own cyber fraud gang.
Police claim he established contacts through:
- Facebook
- Social media platforms
- Online fraud networks
- Telegram groups
These networks allegedly supplied:
- Fake bank accounts
- Fraud SIM cards
- Malware APK files
- Digital payment channels
Investigators suspect the accused may have been connected to a broader organized cybercrime ecosystem operating across several Indian states.
Rise of APK-Based Cyber Fraud in India
Cybersecurity agencies across India have repeatedly warned citizens about the growing use of APK malware scams.
Fraudsters commonly impersonate:
- Banks
- Courier companies
- Government departments
- Electricity boards
- Telecom operators
- Customer support executives
Victims are manipulated into installing harmful applications under the pretext of:
- KYC verification
- Cashback offers
- Delivery tracking
- PAN card updates
- Loan approvals
- Electricity bill payments
Once installed, the malware enables criminals to bypass security systems and steal money in real time.
Common APK Scam Workflow
Financial Cybercrime Trends in India
The incident reflects a broader national trend where cybercriminals are shifting from traditional phishing methods to malware-driven attacks.
Major Reasons Behind the Increase
| Factor |
Impact |
| Rapid smartphone adoption |
Larger target base |
| Increased digital banking |
More online transactions |
| Low cyber awareness |
Easier victim targeting |
| Third-party APK installations |
Security vulnerabilities |
| Social engineering tactics |
Higher success rate |
Law enforcement agencies have observed that many cybercrime operations are now functioning like organized businesses with defined roles, including:
- Data collectors
- Social engineers
- Account suppliers
- Technical malware operators
- Money handlers
Police Investigation Continues
Police officials stated that under interrogation pressure, the accused allegedly transferred the victim’s ₹2.48 lakh back into the bank account.
Authorities are now attempting to identify:
- Additional gang members
- Source of malware tools
- Financial transaction networks
- Other linked bank accounts
- Additional victims across India
Investigators believe more arrests may follow in the coming weeks.
Digital forensic experts are also analyzing the recovered devices to determine whether the accused was involved in:
- SIM swapping
- Banking trojans
- Remote access attacks
- OTP interception scams
Cyber Safety Measures for Citizens
Cybersecurity experts advise users to remain extremely cautious while downloading applications outside official app stores.
Important Safety Tips
Never Install Unknown APK Files
Only download apps from trusted platforms like the Google Play Store.
Avoid Clicking Suspicious Links
Do not open APK files received through WhatsApp, SMS, Telegram, or social media.
Check App Permissions Carefully
Be cautious if an app requests:
- SMS access
- Accessibility permissions
- Screen recording access
- Contact permissions
Enable Banking Alerts
Instant SMS and email notifications can help detect unauthorized transactions quickly.
Use Multi-Factor Authentication
Additional security layers reduce the risk of account compromise.
Report Fraud Immediately
Victims should report cybercrime incidents through:
- NCRP portal
- Local cyber police stations
- Bank helplines
Conclusion
The arrest of the Bihar-based accused by Delhi Police underscores the evolving nature of cybercrime in India, where malware-based APK scams are becoming increasingly sophisticated and financially damaging.
The case not only exposes the methods used by cybercriminal networks but also highlights the urgent need for stronger cyber awareness among digital banking users.
As India rapidly expands its digital economy, experts warn that cyber hygiene, public awareness, and coordinated law enforcement efforts will play a critical role in preventing such technologically advanced financial crimes in the future.
Follow cyberdeepakyadav.com on