India’s Emerging Cyber Crime Corridor: The Nuh–Madhya Pradesh Nexus and Its National Security Implications
A detailed analysis of the ₹3,000 crore cyber crime network linking Nuh (Haryana) and Madhya Pradesh, highlighting fraud mechanisms, mule accounts, and potential national security risks.

Cyber Crime Corridor: The Emerging Nexus Between Nuh
(Haryana) and Madhya Pradesh

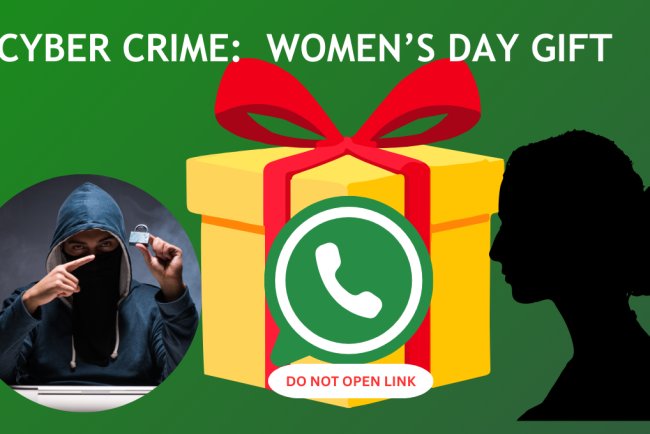
A significant cyber crime network has emerged linking Nuh district in Haryana with multiple regions in Madhya Pradesh. What initially appeared as isolated fraud cases has evolved into a highly organized, multi-layered criminal ecosystem involving financial fraud, identity misuse, and potential international fund transfers. The scale and sophistication of this network raise concerns not only about law enforcement capacity but also about broader national security implications.
Background and Context
Nuh, located in southeastern Haryana, has historically faced socio-economic challenges such as unemployment, limited education, and weak policing infrastructure. In recent years, it has gained notoriety as a major cyber crime hub, surpassing earlier hotspots like Jamtara in both scale and operational complexity.
Simultaneously, Madhya Pradesh has emerged as a critical support base for these operations, particularly in providing financial and logistical channels.
Scale of the Fraud
- Estimated fraud value: Over ₹3,000 crore
- Time period: Less than two years
- Number of mule accounts: 1,000+
- Affected regions: Pan-India, with international fund transfers
Investigations revealed that although financial activity was traced in Madhya Pradesh, the masterminds operated primarily from Nuh, often using urban centers like Gurugram as operational bases.
Operational Structure of the Network

1. Illegal Call Centers
Fraud operations were coordinated through unauthorized call centers, where individuals—often young school dropouts—executed scams across India. Common fraud types included:
- Job scams
- Investment and cryptocurrency fraud
- Impersonation of law enforcement agencies
- “Digital arrest” threats
2. Mule Bank Accounts
A large number of bank accounts belonging to economically vulnerable villagers were used to route illicit funds.
- Account holders were misled with promises of government benefits
- Accounts were rented for small monthly payments
- Transactions worth crores passed through these accounts
3. SIM Card Supply Chain
Fake or illegally obtained SIM cards formed the backbone of communication.
Supply chain flow:
Madhya Pradesh → Patna → Nuh
These SIM cards enabled anonymity and scalability in fraudulent operations.
4. Shell Companies and Money Laundering
Shell companies established in cities like Hyderabad and parts of Maharashtra were used to:
- Layer transactions
- Conceal the origin of funds
- Facilitate large-scale money movement
5. International Transfers
Investigators confirmed that a portion of the funds was routed abroad, particularly to the Middle East. The exact purpose of these transfers remains under investigation.
Human and Social Impact
The consequences of these crimes extend beyond financial loss:
- Victims subjected to psychological manipulation and fear
- Cases of prolonged intimidation (“digital arrest”)
- Financial ruin of individuals and families
- A reported suicide linked to reputational distress caused by fraud accusations
These incidents highlight the psychological dimension of cyber crime, where fear is used as a primary tool.
Law Enforcement Challenges
Data indicates systemic limitations:
- Total reported fraud (MP): ₹1,054 crore
- Recovery: Less than 1%
- High volume of complaints with low charge-sheet conversion
Challenges include:
- Lack of technical expertise
- Interstate coordination gaps
- Slow investigative processes
Key Analytical Chart
Cyber Crime Ecosystem Model
| Component | Location/Source | Function | Impact |
|---|---|---|---|
| Mastermind Operations | Nuh (Haryana) | Planning and coordination | Central control of network |
| Call Centers | Gurugram | Execution of fraud calls | Victim targeting nationwide |
| Mule Bank Accounts | Madhya Pradesh villages | Money routing and laundering | Financial masking |
| SIM Card Network | MP → Patna → Nuh | Anonymous communication | Operational scalability |
| Shell Companies | Hyderabad, Maharashtra | Fund layering and legitimacy | Money laundering |
| Victims | Across India | Targets of fraud | Financial and psychological loss |
| International Channels | Middle East (suspected) | Fund transfers | Potential global linkage |
Critical Observations
- Decentralized but Connected Network
The system operates across multiple states but remains centrally coordinated. - Exploitation of Vulnerability
Economically weaker populations are used as tools within the system. - Technological Misuse
Digital infrastructure (banking, telecom) is being exploited at scale. - Low Deterrence
Minimal recovery rates reduce the perceived risk for criminals.
Concerns and Limitations
While the article presents a strong case, certain aspects require caution:
- The link to terror financing remains unconfirmed and under investigation
- Some regional generalizations may overstate the involvement of entire districts
- Data presentation lacks clarity in differentiating total fraud vs regional impact
Conclusion
The Nuh–Madhya Pradesh cyber crime nexus represents a shift from localized fraud to an organized, multi-state criminal industry. It combines financial exploitation, technological misuse, and psychological manipulation at scale.
Addressing this issue will require:
- Stronger interstate coordination
- Enhanced cyber policing capabilities
- Financial system safeguards
- Public awareness against digital fraud tactics
The situation underscores the urgent need for systemic reforms to counter increasingly sophisticated cyber threats.
Follow cyberdeepakyadav.com on
Facebook, Twitter, LinkedIn, Instagram, and YouTube
What's Your Reaction?