Tag: malware
Don’t Just Scan That QR Code: An Ethical Hacker’s ...
Rupali Shukla Aug 30, 2025 0 307
In the world we live in, convenience is paramount. Do you want to settle your bill? Take a look at the QR code. Do you want to ...
Malware Forensics: Dissecting Modern Ransomware & ...
DEEPAK YADAV Aug 25, 2025 0 381
Malware forensics is the study of harmful software to determine how it functions, how it got into a system, and what harm it did. ...
2.3 Million Users Infected by Malicious Chrome & E...
DEEPAK YADAV Jul 10, 2025 0 369
For years at a time, 18 extensions had a "squeaky clean" codebase until a version bump made them into malicious trojans without an...
How to Avoid Malicious APKs on Your Android Phone?
Shashank dave Apr 30, 2025 0 1128
Android apps install via APK files, but some “malicious APKs” hide dangerous software that can steal your data, spy on you, or eve...
WhatsApp Wedding Card Downloads Can Delete Your Da...
preeti Nov 12, 2024 0 408
Beware of downloading wedding cards from WhatsApp this season. Some digital wedding invitations contain malicious links or attachm...
Popular Posts
-
Whatsapp Helpline: Guide to Reporting WhatsApp’s Griev...
Rupali Shukla Jul 14, 2025 13 7454
-
Instagram helpline : A Complete Guide to Instagram Comp...
DEEPAK YADAV Jul 13, 2025 1 6441
-
Amroha Police Cyber Security Internship Program - 2025
DEEPAK YADAV May 20, 2025 1 5213
-
Cyber Security Summer Internship Gurugram Police 2025 1...
DEEPAK YADAV May 1, 2025 0 4453
-
Bank Account Unfreeze : Application for Reactivating Fr...
Rupali Shukla Jul 21, 2025 1 3778
Our Picks
-
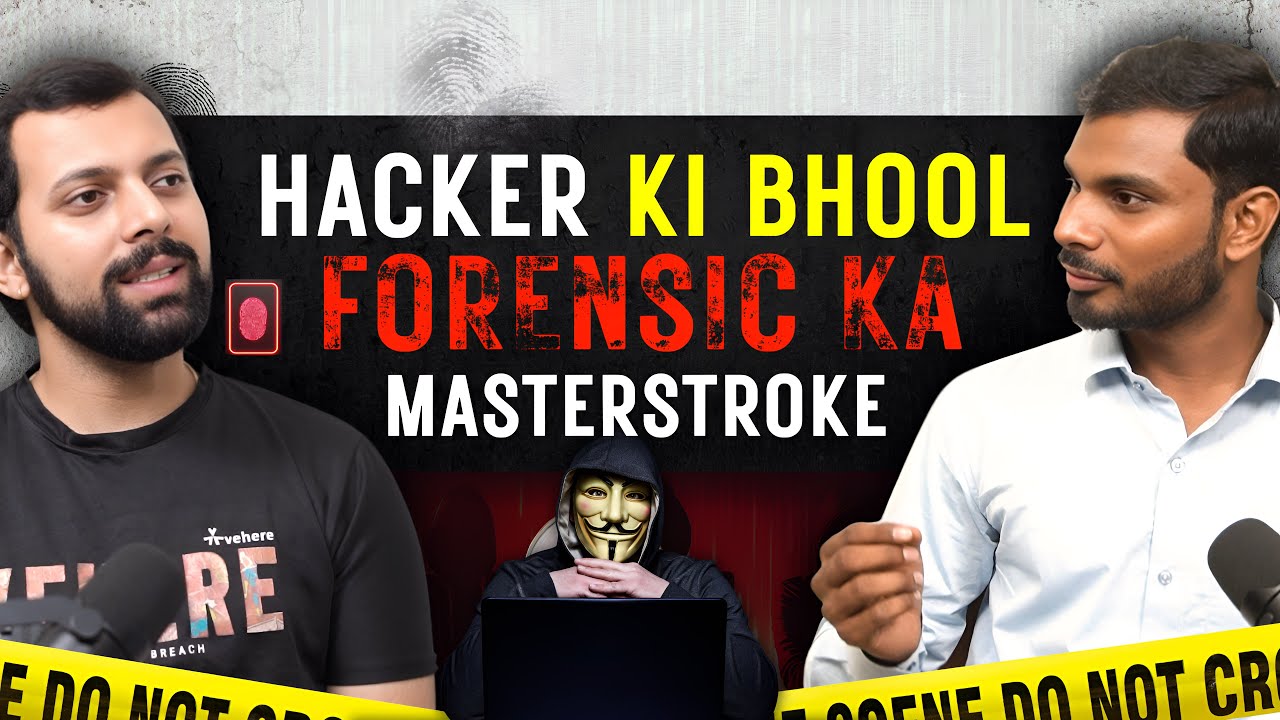
Hacker ki Galti- Forensic Expert Ka Masterstoke || Ft. ...
DEEPAK YADAV May 27, 2026 0 29
-
Password Strong Nahi...aapka mindset Strong hona Chahiy...
DEEPAK YADAV Dec 30, 2025 0 769
-
State/UT Nodal Officer and Grievance Officer contact de...
DEEPAK YADAV Aug 21, 2025 1 1332
-
Case 1 - Cheap stuff
Rupali Shukla Aug 5, 2025 0 506
-
Bank Account Unfreeze : Application for Reactivating Fr...
Rupali Shukla Jul 21, 2025 1 3778
Categories
- Cyber Crime(124)
- Help Line(19)
- Seminars(2)
- Case Study(13)
- Trending Crime(24)
- Nodal Officer(1)
- News(244)
- Cyber News(203)
- Technology News(9)
- Latest Updates(31)
- Podcast(11)
- Blog(113)
Random Posts
Voting Poll
What is a hash function used for in digital forensics?
Total Vote: 5
Encrypting files
What does ‘write blocker’ do in forensics?
Total Vote: 6
Allows writing on drives
The most common method for identifying a person is:
Total Vote: 6
Blood type
Which of the following is an example of physical evidence?
Total Vote: 10
A confession letter
What is chain of custody?
Total Vote: 11
A prisoner's handcuff
Who is considered the "Father of Forensic Science"?
Total Vote: 8
Sir Arthur Conan Doyle
Which of these is a sign of a secure website?
Total Vote: 9
The page loads fast
What is 2FA (Two-Factor Authentication)?
Total Vote: 9
Logging in with two devices
What is the most important first step when collecting digital evidence from a suspect’s device?
Total Vote: 8
Turn off the device to preserve battery life
What is phishing?
Total Vote: 9
A method to catch fish online