Social Media Forensics || Cyber Deepak Yadav
Social media forensics is a specialized domain of digital forensics that focuses on extracting and analyzing data from online social platforms to support investigations, intelligence gathering, and legal proceedings. Platforms commonly investigated include Facebook, Instagram, Twitter (X), WhatsApp, and Telegram.
1. Nature of Social Media Evidence
Social media data is dynamic, distributed, and user-generated, making it very different from traditional digital evidence.
Characteristics:
- Volatile → Stories and disappearing messages
- Massive scale → Millions of interactions
- Heterogeneous → Text, images, videos, reactions
- Cloud-based → Stored on remote servers
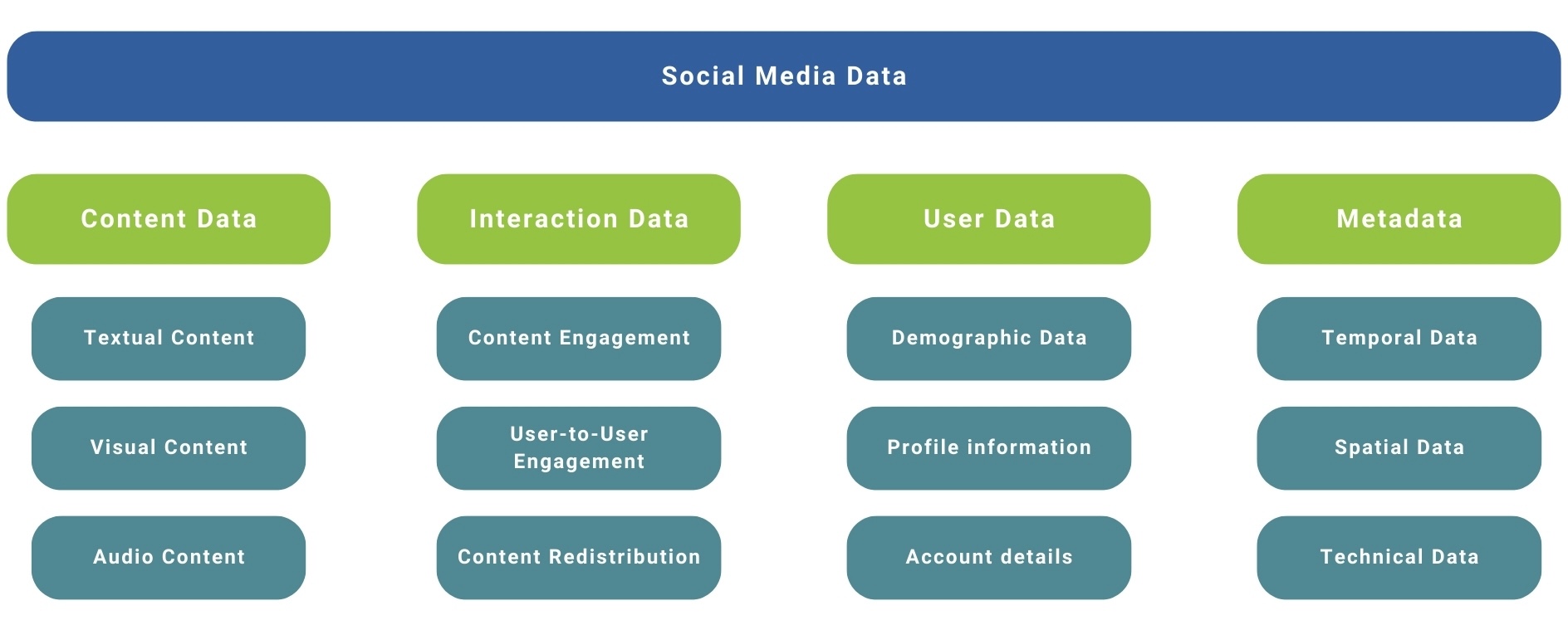
2. Types of Social Media Data (Deep Classification)
A. Content Data
- Posts, captions, tweets
- Comments and replies
- Hashtags and mentions
B. Communication Data
- Direct messages (DMs)
- Group chats
- Voice/video calls (logs)
C. Multimedia Data
- Photos, videos, reels, stories
- Live streams
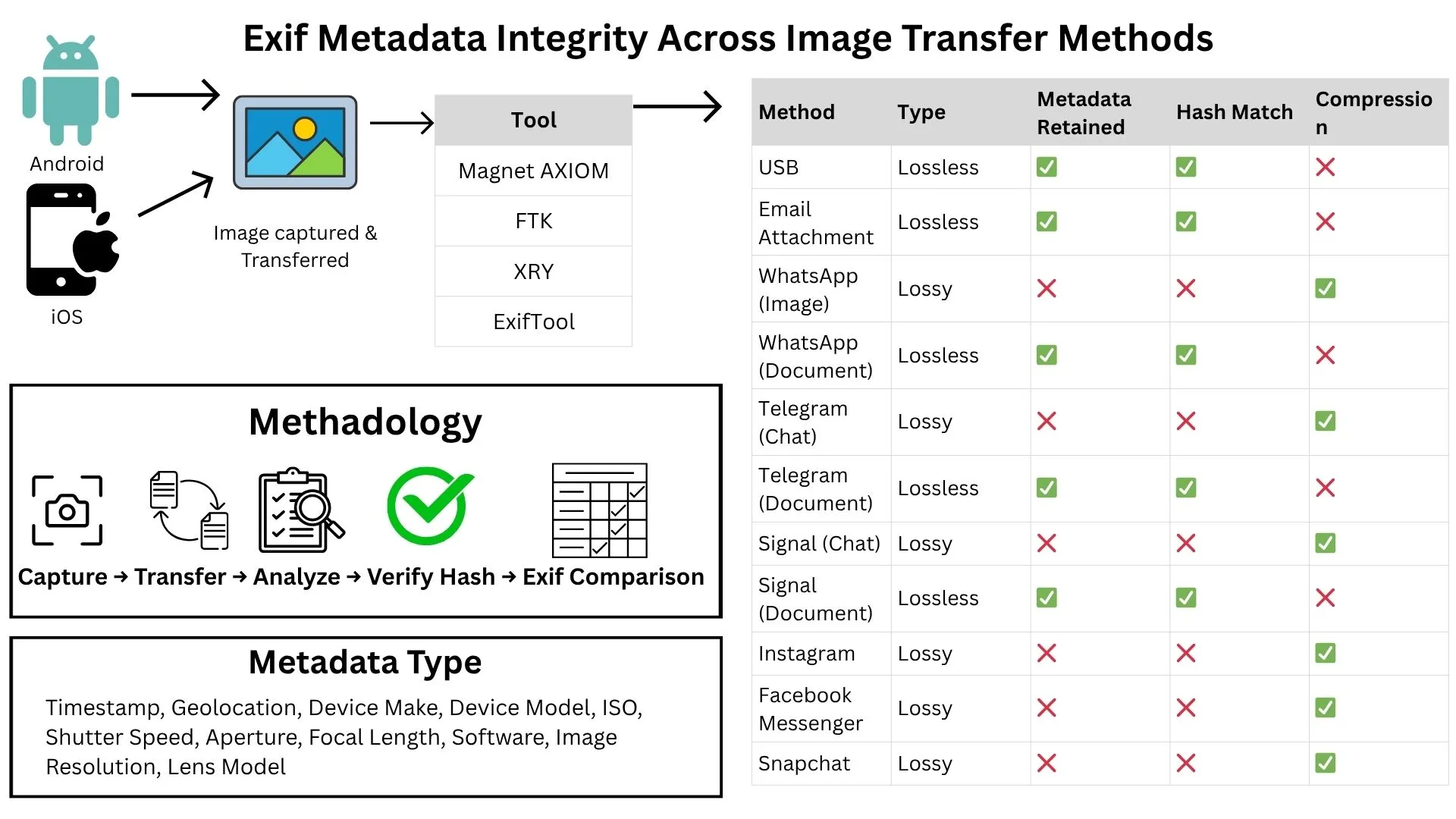
D. Metadata (Critical Evidence Layer)
- Timestamp (creation/modification)
- Geolocation (latitude/longitude)
- Device information (OS, IP address)
- EXIF data from images
E. Social Graph Data
- Friends/followers
- Interaction patterns
- Network connections

3. Complete Investigation Process
Step 1: Identification
- Identify relevant accounts, posts, or conversations
- Detect fake or multiple accounts
Step 2: Acquisition (Collection)
Methods:
- API-based extraction (official platform access)
- Web scraping (with legal permission)
- Forensic tools
- Manual capture (screenshots) → least reliable
Key Issue:
Data must be collected without altering original evidence
Step 3: Preservation
- Create forensic images or copies
- Generate hash values (MD5/SHA) to ensure integrity
- Maintain chain of custody documentation
Step 4: Examination & Analysis
Techniques:
- Timeline reconstruction
- Keyword filtering
- Sentiment analysis
- Behavioral profiling
- Link/network analysis
Example:
Using Maltego to visualize connections between suspects.
Step 5: Reporting
- Findings presented in structured reports
- Must include:
- Methodology
- Tools used
- Evidence authenticity
- Used in courts or cybercrime investigations
4. Advanced Analytical Techniques
1. OSINT (Open Source Intelligence)
- Collect publicly available data
- Includes:
- Public profiles
- Comments and hashtags
- Location tags
2. Network Analysis
- Maps relationships between users
- Detects:
- Criminal groups
- Influencers
- Hidden connections
3. Linguistic & Sentiment Analysis
- Detects:
- Threats
- Hate speech
- Radicalization patterns
4. Image & Video Forensics
- Reverse image search
- Deepfake detection
- Metadata extraction
5. Geolocation Analysis
- Identifies location from:
- GPS tags
- Background objects
- Landmarks
5. Specialized Tools
- X1 Social Discovery → Data extraction
- Hunchly → Web evidence logging
- Maltego → Link analysis
- Autopsy → Evidence analysis
- Magnet AXIOM → Advanced investigations
- Cellebrite Inseyets → Data extraction and analysis
6. Challenges (Deep Understanding)
A. Encryption & Privacy
- End-to-end encryption in apps like Signal
- Limited access to message content
B. Ephemeral Content
- Stories disappear in 24 hours
- Difficult to capture in time
C. Fake Identities
- Bots and anonymous profiles
- Deepfake-generated accounts
D. Legal Jurisdiction
- Data stored across countries
- Requires international cooperation
E. Big Data Problem
- Huge volume → requires automation
7. Legal & Ethical Framework
Key Principles:
- Authorization (warrants/legal permission)
- Privacy protection
- Evidence integrity
- Admissibility in court
Important Concept:
Chain of Custody
- Tracks who handled evidence
- Ensures no tampering
Follow cyberdeepakyadav.com on
Facebook, Twitter, LinkedIn, Instagram, and YouTube
What's Your Reaction?