Dark Web Forensics — Deep Dive
Let’s go beyond basics and break Dark Web Forensics into technical layers, methodologies, workflows, and real investigative strategies.
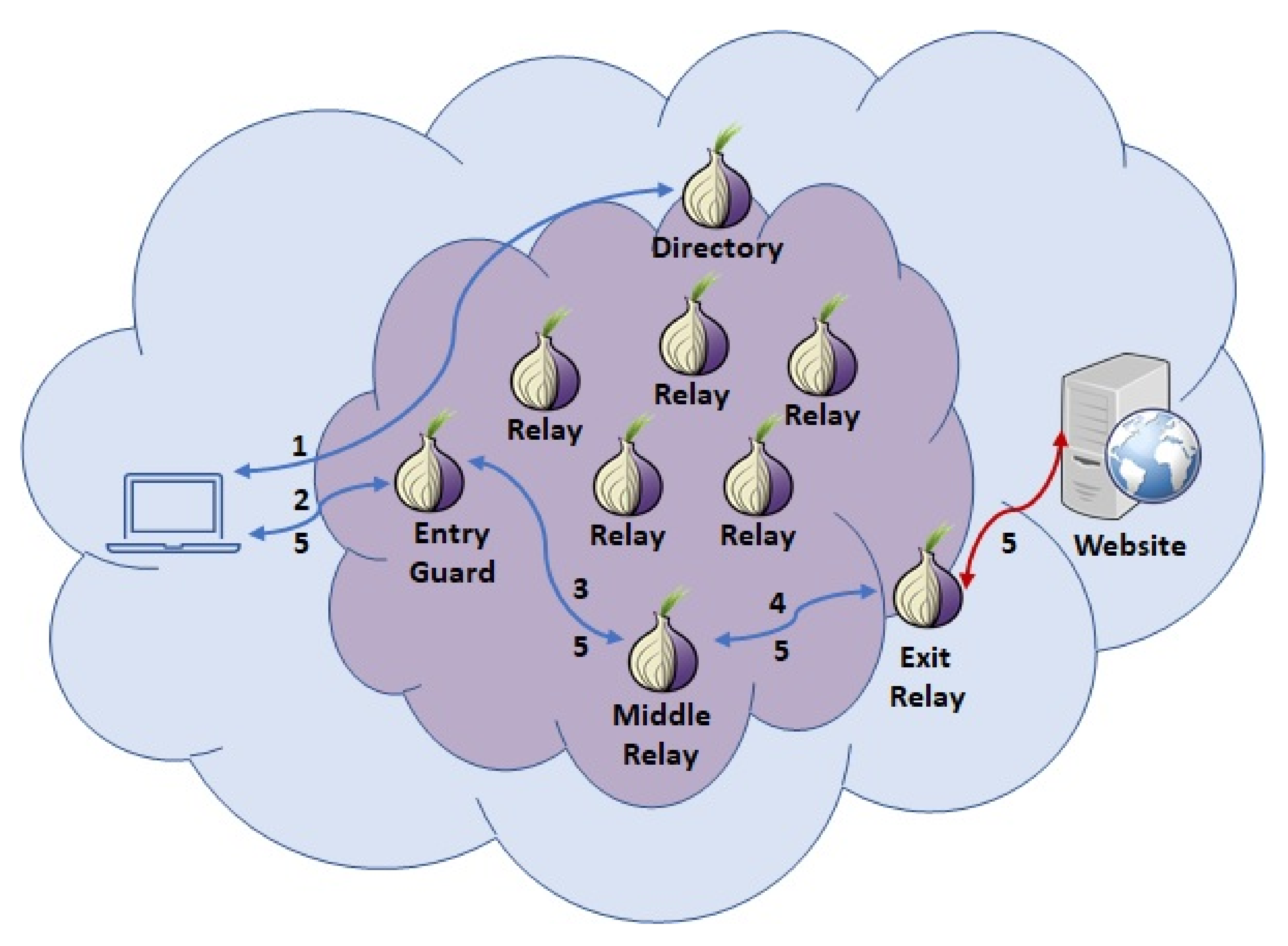
Architecture of the Dark Web (Technical Foundation)
How Tor Actually Works
The dark web relies heavily on Tor (The Onion Router).
Onion Routing Process
- Data is wrapped in multiple encryption layers
- Sent through 3+ random nodes:
- Entry Node
- Relay Node
- Exit Node
- Each node decrypts only one layer → cannot trace full path
Result: Source and destination are separated
Hidden Services (.onion sites)
- No exit node needed
- Both user and server stay anonymous
- Uses rendezvous points
Dark Web Forensic Investigation Lifecycle
Step-by-Step Workflow
1. Intelligence Gathering
- Crawl dark web forums/markets
- Use OSINT tools like Maltego
- Collect:
- Usernames
- PGP keys
- Email leaks
2. Data Acquisition
- Capture volatile and non-volatile data
- Techniques:
- Memory dumps
- Packet captures
- Server seizures (if possible)
3. Preservation of Evidence
- Maintain chain of custody
- Use hashing (MD5/SHA256) to ensure integrity
4. Analysis Phase

Multi-layer Analysis:
A. Network Forensics
- Tools like Wireshark
- Analyze traffic patterns (timing correlation attacks)
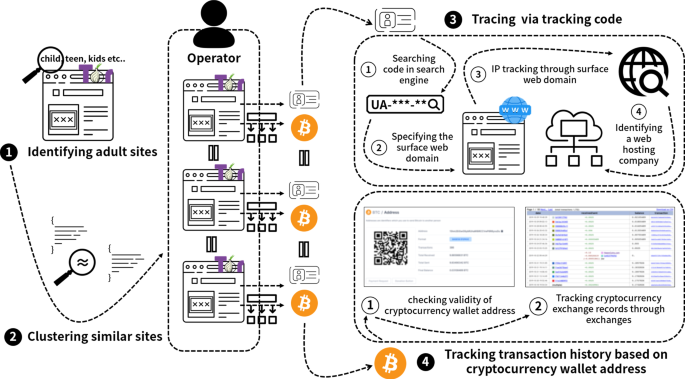
B. Cryptocurrency Forensics
- Track Bitcoin transactions:
- Address clustering
- Transaction graph analysis
- Mixing detection
C. Malware Analysis
- Reverse engineering ransomware, trojans
- Sandbox execution
D. Behavioral Analysis
- Writing style (stylometry)
- Login patterns
- Vendor reputation analysis
Attribution (Hardest Step)
Linking:
- Online pseudonym → real identity
Methods:
- IP leaks
- Reused usernames
- Metadata mistakes
- Payment trails

Advanced Techniques Used
A. Traffic Correlation Attacks
Even though Tor hides identities:
- Investigators monitor entry + exit traffic timing
- Match patterns → deanonymization
B. Blockchain Forensics (Deep Level)
Key Concepts:
- UTXO model (Unspent Transaction Output)
- Address clustering heuristics
- Taint analysis
Example:
- One wallet interacts with multiple known illegal addresses → cluster formed
C. Stylometry (Linguistic Forensics)
- Analyze writing style:
- Grammar
- Vocabulary
- Sentence patterns
Used to identify authors behind aliases.
D. Metadata Exploitation
Files uploaded on dark web may contain:
- GPS data
- Device info
- Author name
E. Honeypots
- Fake marketplaces or forums set up by investigators
- Attract criminals → collect data
Real Challenges (Technical Depth)
1. End-to-End Encryption
Even if traffic is captured → content unreadable
2. Cryptocurrency Obfuscation
- Mixers (Tumblers)
- Privacy coins (Monero, Zcash)
3. Distributed Infrastructure
Servers hosted across multiple jurisdictions
4. Ephemeral Ecosystem
- Sites frequently shut down
- Mirror links appear instantly
Professional Tool Ecosystem
Investigation Tools
- Maltego → link analysis
- Autopsy → disk forensics
Network Tools
- Wireshark
- TCPDump
Blockchain Tools
- Chainalysis
- Elliptic
- CipherTrace
Skills Required
- Networking (TCP/IP, DNS, routing)
- Cryptography basics
- Programming (Python, C++)
- Cybersecurity concepts
- Legal knowledge

Follow cyberdeepakyadav.com on
Facebook, Twitter, LinkedIn, Instagram, and YouTube
What's Your Reaction?