Mobile, IoT & Wearable Forensics
Mobile, IoT, and wearable forensics fall under “pervasive digital forensics” — where evidence is: Distributed (across devices, networks, cloud) Heterogeneous (different formats, OS, vendors) Ephemeral (short-lived data) Unlike traditional computer forensics, here: Evidence is not centralized Investigators must reconstruct ecosystems, not just devices
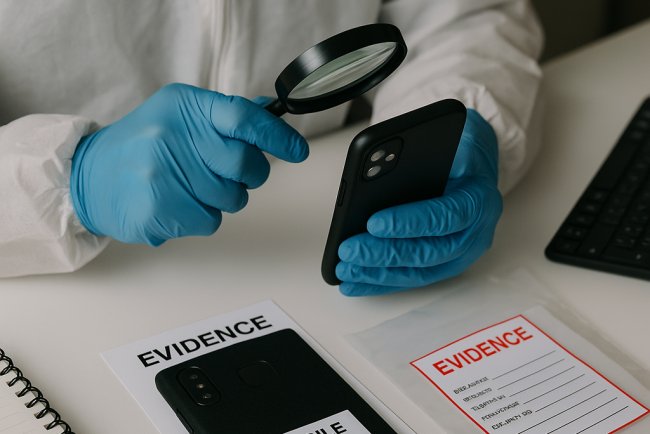
Mobile Forensics — Deep Dive
A. Levels of Data Acquisition
Mobile forensic extraction happens at different depths:
1. Logical Extraction
- Accesses data via OS APIs
- Fast but limited
- Example: contacts, messages
2. File System Extraction
- Retrieves full file structure
- Includes hidden/system files
3. Physical Extraction (Most Powerful)
- Bit-by-bit copy of device memory
- Recovers deleted data
4. Advanced Methods
- JTAG → direct memory access via hardware pins
- Chip-off → physically removing memory chip
These are used when devices are locked or damaged

B. Types of Mobile Artifacts
- Application artifacts (WhatsApp DB, Telegram cache)
- System artifacts (logs, temp files)
- Location artifacts
- GPS
- Wi-Fi triangulation
- Cell tower logs
- Metadata
- EXIF (image timestamps, coordinates)
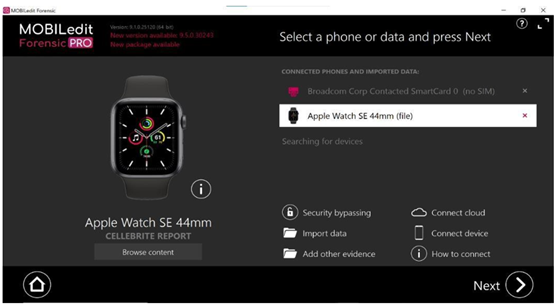
C. Tools Used
- Cellebrite UFED
- Oxygen Forensics
- Magnet AXIOM
- Autopsy (open-source)
D. Advanced Challenges
- Secure Enclave (iOS)
- Full disk encryption
- App sandboxing
- Remote wipe features
IoT Forensics — Deep Dive
A. IoT Forensic Architecture
IoT evidence exists in three layers:
1. Device Layer
- Sensors, firmware, local logs
- Example: smart lock entry logs
2. Network Layer
- Router logs
- Packet captures (Wireshark)
3. Cloud Layer
- Vendor servers (AWS, Google Cloud)
- Stores majority of data
Investigators must correlate across all three

B. Evidence Sources
- Event logs (on/off events)
- Voice assistant recordings
- Camera footage
- Device pairing logs
- Firmware data
C. Forensic Techniques
1. Live Forensics
- Capturing volatile data while device is running
2. Network Forensics
- Monitoring traffic between IoT and servers
3. Cloud Forensics
- Legal requests to service providers
D. Major Challenges
- No standard OS (unlike Windows/Android)
- Proprietary ecosystems (Amazon, Google, Xiaomi)
- Limited storage → data overwritten quickly
- Legal barriers (data stored in other countries)

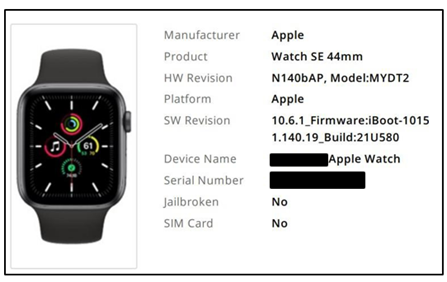
Wearable Forensics — Deep Dive
A. Types of Wearable Data
1. Physiological Data
- Heart rate
- Calories burned
- Oxygen levels
2. Activity Data
- Steps
- Movement patterns
3. Location Data
- GPS routes
- Distance tracking

B. Data Dependency
Wearables rarely store full data locally:
Data flows:
Wearable → Smartphone → Cloud
So investigators must analyze:
- Watch
- Paired phone
- Cloud account
C. Forensic Value
Wearables are powerful because they:
- Provide objective biological evidence
- Cannot be easily manipulated (in many cases)
Example Uses
- Determining time of death
- Verifying alibi (movement vs claim)
- Detecting sudden physical activity (struggle)
Evidence Correlation & Timeline Reconstruction
Core Idea
Modern forensics = timeline reconstruction
Multi-Device Correlation Example:
| Device | Evidence |
|---|---|
| Phone | GPS shows suspect near location |
| IoT Camera | Records entry at 8:45 PM |
| Wearable | Heart rate spike at 8:47 PM |
Combined → high-confidence narrative
Legal & Ethical Considerations
- Chain of custody (evidence integrity)
- Data admissibility in court
- Privacy laws (GDPR, etc.)
- Consent & surveillance issues
Example issue:
Can Alexa voice logs be used as legal evidence?
Emerging Trends
1. AI in Device Analysis
- Automated artifact extraction
- Pattern recognition across devices
2. Edge Computing Forensics
- Data processed locally (harder to collect)
3. Anti-Forensics Techniques
- Data obfuscation
- Secure deletion
4. Smart Vehicles & IoT Expansion
- Cars becoming major forensic sources
Follow cyberdeepakyadav.com on
Facebook, Twitter, LinkedIn, Instagram, and YouTube
What's Your Reaction?